Eset Hash Check | 2025 |
In an era defined by sophisticated ransomware, fileless malware, and Advanced Persistent Threats (APTs), cybersecurity often focuses on complex, AI-driven solutions. However, some of the most critical vulnerabilities lie not in elaborate code, but in the integrity of the software we download and install daily. Enter ESET Hash Check , a seemingly simple, lightweight utility that addresses a foundational pillar of digital security: file integrity verification. While not a household name like its parent antivirus suite, ESET Hash Check represents a crucial, user-friendly tool for ensuring that the files on your system are exactly what they claim to be, safeguarding against data corruption, man-in-the-middle attacks, and deliberate file tampering. The Purpose: Beyond the Antivirus Scope ESET is best known for its NOD32 antivirus engine, which uses heuristics and signature-based detection to catch malware. However, traditional antivirus cannot protect against every scenario. For instance, if a legitimate software installer is intercepted during download and replaced with a backdoored version (a common supply chain attack), the antivirus may not flag it immediately if the malicious code is new or well-hidden.
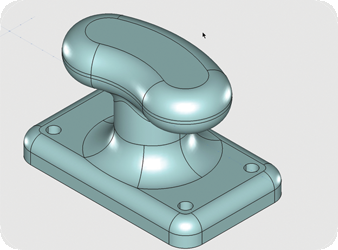
This simplicity is its greatest strength. It lowers the barrier to entry for non-experts. A journalist downloading secure messaging software or a system administrator retrieving a critical patch does not need to learn command-line tools like Get-FileHash in PowerShell or sha256sum in Linux. ESET Hash Check democratizes a forensic-level verification process, making it accessible to any Windows user. The primary strength of ESET Hash Check is its transparency . It does not rely on a cloud database or “reputation scores.” It performs local, mathematical computation. This means it works offline and is immune to server-side compromises. If a hacker compromises the official website but fails to update the listed hash, the tool will still catch the discrepancy. eset hash check
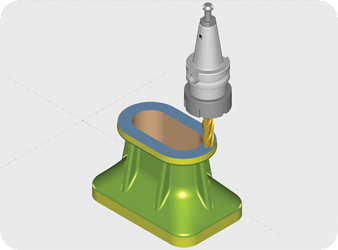
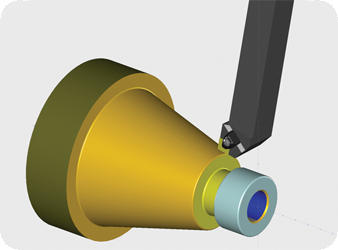
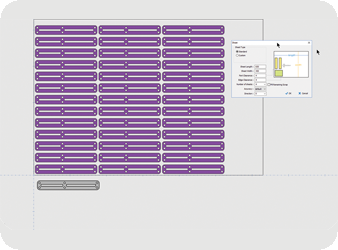
The Hash Check utility was designed to fill this gap. Its primary function is to compute and compare cryptographic hash values—typically MD5, SHA-1, and SHA-256—of a given file. A hash is a unique digital fingerprint; even a single bit change in the file produces a completely different hash. By allowing users to compare a file’s calculated hash against an official hash provided by the software publisher, ESET Hash Check provides a binary, undeniable answer: Core Functionality and User Experience The utility is a testament to minimalist design. Unlike bloated security suites, ESET Hash Check is a portable executable (requiring no installation) with a drag-and-drop interface. To use it, a user downloads a file (e.g., a Linux ISO or a firmware update) and navigates to the publisher’s website to find the official SHA-256 checksum. The user then drags the downloaded file into the Hash Check window. Instantly, the tool displays the file’s hash in multiple formats. A quick visual comparison—or a copy-paste into a comparison field—confirms integrity. In an era defined by sophisticated ransomware, fileless