October 2, 2025

A variety of malicious payloads delivered through similar fake invitations
[ f'(x) = \lim_h \to 0 \fracf(x+h) - f(x)h ]
Take ( \ln ) of both sides, use log properties to simplify, differentiate implicitly, solve for ( y' ).
Find the derivative of ( f(x) = x^2 ).
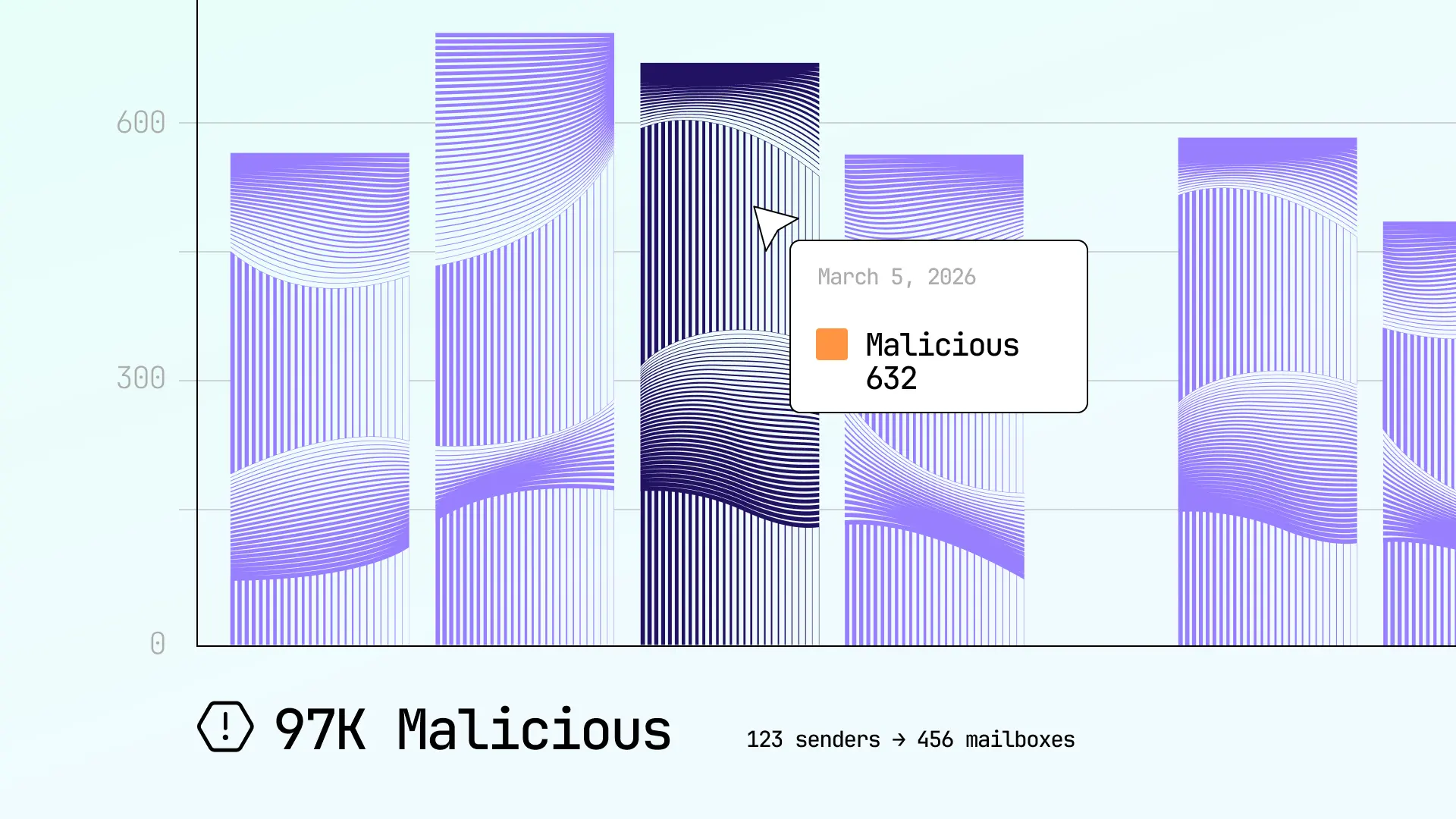
Enhanced reporting and analytics provide complete visibility into email security calculo de derivadas
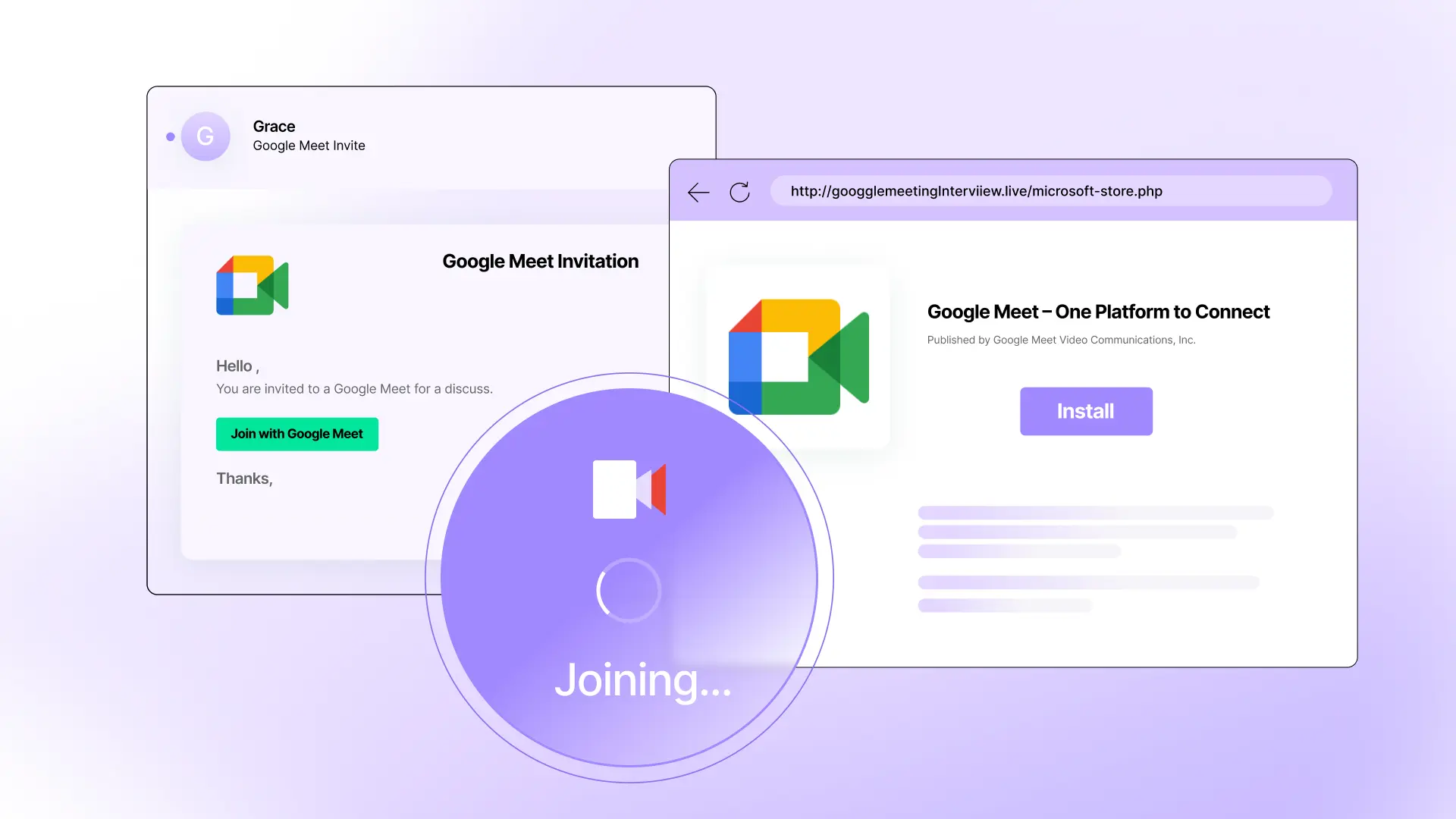
Fake Google Meet invitation, fake Microsoft Store, real malware attack [ f'(x) = \lim_h \to 0 \fracf(x+h) -


See how Sublime delivers autonomous protection by default, with control on demand.
.svg)